- Joined
- Nov 15, 2007
- Messages
- 854
- Solutions
- 10
- Reaction score
- 389
- Location
- Santiago, Chile (Australian)
Proxy Tunnel Solution | With Client IP Passthrough
Written by Michael Orsino for dura-online who have kindly chosen to contribute this back to the community
Difficulty level: Medium - this guide assumes some linux & firewall knowledge
Reading time: 4 minutes
What is this?
A solution for setting up a forward proxy to tunnel connections, respecting the original IP address of the client.
Why do I need this?
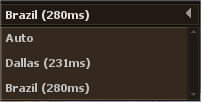
Strategically located forward proxy tunnels may improve the latency and reliability of connections to your services. (this is not the place to debate that - tire yourself out on reddit instead please). The solutions provided in this guide are also applicable for security and load balancing configurations.
Typically in these configurations the IP address of the client is lost and the service can only see the IP address of the proxy server itself. This is problematic for a few reasons such as logging; moderation; server list reporting; mc checking.
With this solution the IP address of the client is respected and all features of the service will operate as usual.
How does it work?
It is indistinguishable from magic.
If you're interested on a technical networking level, check out this cloudflare blog post.
Are there alternatives?
Yes, there are alternative solutions to this problem and also different ways of configuring this solution. I believe this to be both the simplest in terms of deployment and best in terms of maximum connections and Mbps throughput.
The cloudflare article linked above talks about some of the alternatives.
One notable alternate solution is to pay Kondrah USD$1500 for his system, but I cannot speak to how well it works.
1.) Prerequisites
For your forward proxy server I'll provide instructions for two options: #1 HAProxy; #2 NGINX.
Which should you use? If you're already using NGINX for something else, use it for this too. If not, use HAProxy.
Preliminary
$
$
$
Option #1: HAProxy
$
$
$
$
$
$
$
$
$
$
$
$
$
- Press
The go-mmproxy invocation command looks a little intimidating at first, but it is actually pretty straight forward. You can read more about the individual switches here.
Thats all folks! I hope this guide proves to be useful for some people either in an otserv application or even for their real life jobs as this guide has application far beyond otserv hosting!
If you find this guide useful and especially if it saves you USD$1500 please consider buying me a coffee!
Credits:
Path Network for creating the go-mmproxy utility this guide relies on;
Michael for writing this guide;
Dura Online for releasing it to the community.
Written by Michael Orsino for dura-online who have kindly chosen to contribute this back to the community
Difficulty level: Medium - this guide assumes some linux & firewall knowledge
Reading time: 4 minutes
What is this?
A solution for setting up a forward proxy to tunnel connections, respecting the original IP address of the client.
Why do I need this?
Strategically located forward proxy tunnels may improve the latency and reliability of connections to your services. (this is not the place to debate that - tire yourself out on reddit instead please). The solutions provided in this guide are also applicable for security and load balancing configurations.
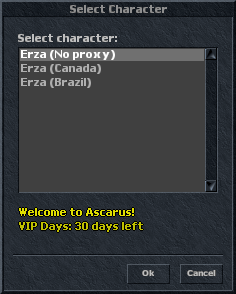
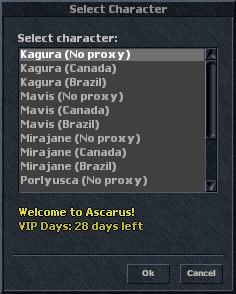
Typically in these configurations the IP address of the client is lost and the service can only see the IP address of the proxy server itself. This is problematic for a few reasons such as logging; moderation; server list reporting; mc checking.
With this solution the IP address of the client is respected and all features of the service will operate as usual.
How does it work?
It is indistinguishable from magic.
If you're interested on a technical networking level, check out this cloudflare blog post.
Are there alternatives?
Yes, there are alternative solutions to this problem and also different ways of configuring this solution. I believe this to be both the simplest in terms of deployment and best in terms of maximum connections and Mbps throughput.
The cloudflare article linked above talks about some of the alternatives.
One notable alternate solution is to pay Kondrah USD$1500 for his system, but I cannot speak to how well it works.
1.) Prerequisites
- Game server running on Linux (This guide will assume Ubuntu 20.04)
- A secondary Linux server to be the proxy (e.g. $10/month DDoS protected VPS)
- Necessary ports opened in the firewalls of both servers. You can use whatever you like, but for this guide we will use the following:
- Game server: 7172 TCP (TFS game), 7173 TCP (proxy listener)
- Proxy server: 7172 TCP (proxy listener)
For your forward proxy server I'll provide instructions for two options: #1 HAProxy; #2 NGINX.
Which should you use? If you're already using NGINX for something else, use it for this too. If not, use HAProxy.
Preliminary
$
sudo apt update$
sudo apt-get update$
sudo apt upgradeOption #1: HAProxy
$
sudo apt install haproxy$
sudo vim /etc/haproxy/haproxy.cfg- Press
shift+gto jump to the last line of the file and then press$to jump to the end of the line. Alternatively use the arrow on your keyboard until you reach the end of the last line - Press the letter
ion your keyboard to switch to insert mode - Type in the following, replacing
123.456.78.9with the IP of your actual game server
Code:
listen game
bind 0.0.0.0:7172
mode tcp
server game 123.456.78.9:7173 send-proxy- Pres the
Esckey to turn off insert mode - Press the
colonkey (shift+;on a U.S. keyboard layout) to enable command mode - Type in
wqandpress enter
/etc/init.d/haproxy restart- If you need to add additional listeners, simply provide a new config for it underneath with a unique listen name e.g.
listen logininstead oflisten game
$
sudo apt install nginx$
sudo vim /etc/nginx/nginx.conf- Press
shift+gto jump to the last line of the file and then press$to jump to the end of the line. Alternatively use the arrow on your keyboard until you reach the end of the last line - Press the letter
ion your keyboard to switch to insert mode - Type in the following, replacing
123.456.78.9with the IP of your actual game server
Code:
stream {
server {
listen 7172;
proxy_pass 123.456.78.9:7173;
proxy_protocol on;
}
}- Pres the
Esckey to turn off insert mode - Press the
colonkey (shift+;on a U.S. keyboard layout) to enable command mode - Type in
wqandpress enter
sudo /etc/init.d/nginx restart- If you need to add additional listeners, simply provide a new config for it underneath inside a new
servertable
$
sudo apt install golang$
go get github.com/path-network/go-mmproxy$
sudo ip rule add from 127.0.0.1/8 iif lo table 123$
sudo ip route add local 0.0.0.0/0 dev lo table 123$
sudo ip -6 rule add from ::1/128 iif lo table 123$
sudo ip -6 route add local ::/0 dev lo table 123$
screen -aS mmproxy$
cd go/bin/$
sudo ./go-mmproxy -l 0.0.0.0:7173 -4 127.0.0.1:7172 -6 [::1]:7172 -p tcp -v 2- Press
ctrl+a+d to detach from this screen sessionThe go-mmproxy invocation command looks a little intimidating at first, but it is actually pretty straight forward. You can read more about the individual switches here.
Thats all folks! I hope this guide proves to be useful for some people either in an otserv application or even for their real life jobs as this guide has application far beyond otserv hosting!
If you find this guide useful and especially if it saves you USD$1500 please consider buying me a coffee!
Credits:
Path Network for creating the go-mmproxy utility this guide relies on;
Michael for writing this guide;
Dura Online for releasing it to the community.
Last edited: